En 2020, Altitude fue adquirida por Enghouse Systems
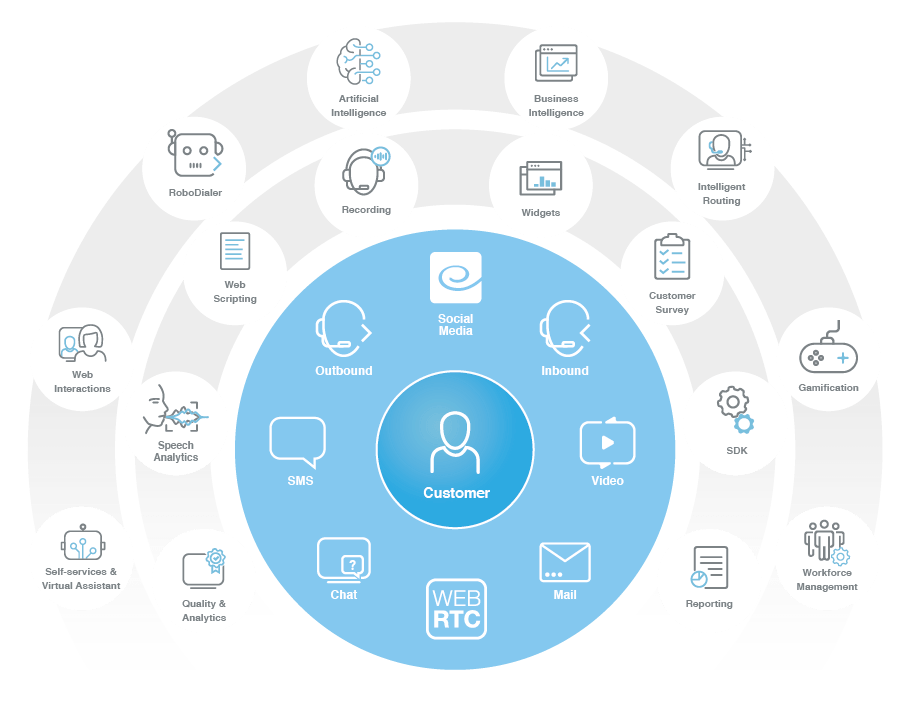
Conoce nuestro portfolio
Contamos con el portfolio más completo para tu Contact Center, para que ofrezcas una atención onmicanal, implementada on-premise o en Cloud.
Smart Staff Optimization (SSO)
Aprovecha las ventajas y oportunidades que trae consigo el teletrabajo para el Contact Center con un paquete de herramientas que te permite gestionar de forma adecuada las operaciones en remoto.

Integra de forma sencilla el canal de vídeo interactivo en tus aplicativos, con la más alta calidad y una resolución de hasta 4K UHD, gracias a la tecnología de vídeo más segura, escalable y personalizable del mercado.
Crea aplicaciones con chat de video multipartitas nativas, móviles y WebRTC.
API y SDK consistentes para integrar rápidamente el canal de video en todas las plataformas.
Recobro
Ofrece autoservicio a través de un asistente virtual, emulando la experiencia de un agente de cobros y siguiendo las mismas reglas de negocio.
BPO
Optimiza los procesos BPO implementando soluciones basadas en tecnología, que permitan mejorar la eficiencia de las operaciones y satisfacer las necesidades de tus clientes.
Telebanca
Mejora la experiencia al cliente, ofreciendo puntos de contacto adicionales a través del canal de vídeo, brindando un servicio personalizado más rápido y eficiente y con una interacción en tiempo real.
Cada conversación aumenta la implicación y comprensión, lo que reduce el tiempo de cada transacción.
Mejora la interacción de cada cliente aumentando la lealtad, confianza y su satisfacción con los procesos y transacciones financieras.